Ways To Keep Customer Data Secure
In our digital age, where data has become a currency of its own, safeguarding customer information is not just a buzzword; it’s an absolute necessity. Imagine your business as a fortress, and customer data as the precious treasure within its walls. Ensuring the security of this treasure is akin to building the most impenetrable fortress, guarded by formidable defenses. In this article, we’ll reveal the ten essential keys to fortify your data fortress, ensuring that your customer’s trust remains unshaken, and your reputation, unblemished.
Implement Strong Access Controls:
 Access control is the foundation of data security. It involves regulating who can access certain parts of your systems and data. To ensure customer data security, businesses must implement strong access controls. This entails:
Access control is the foundation of data security. It involves regulating who can access certain parts of your systems and data. To ensure customer data security, businesses must implement strong access controls. This entails:
Robust Password Policies: Enforce password policies that require employees to create strong, complex passwords that are difficult for attackers to guess. Passwords should be changed regularly, and employees should not reuse passwords across multiple accounts.
Multi-Factor Authentication (MFA): MFA adds an additional layer of security by requiring users to provide two or more forms of identification before granting access. This often includes something the user knows (password) and something the user has (a mobile device or security token).
Role-Based Access Control (RBAC): Implement RBAC to restrict access based on job roles and responsibilities. Employees should only have access to the data and systems necessary for their specific roles. This limits the potential damage if their credentials are compromised.
By combining these elements, businesses can significantly reduce the risk of unauthorized access to customer data.
Encrypt Customer Data:
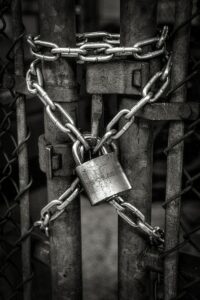
 Encryption is like the lock and key of digital data. It converts data into an unreadable format that can only be decrypted with the appropriate key. There are two primary types of encryption to consider:
Encryption is like the lock and key of digital data. It converts data into an unreadable format that can only be decrypted with the appropriate key. There are two primary types of encryption to consider:
Encryption in Transit: This safeguards data as it moves between systems or over networks. HTTPS (Hypertext Transfer Protocol Secure) is a commonly used encryption protocol for securing web communications. It ensures that data transmitted between a user’s browser and a website’s server is encrypted and secure.
Encryption at Rest: This protects data when it’s stored on devices or servers. It’s crucial to encrypt data at rest to prevent unauthorized access in case physical hardware is stolen or compromised. Encryption tools and techniques vary depending on the platform and storage system being used.
Implementing encryption ensures that even if a data breach occurs, the stolen data remains unintelligible to the attacker, adding an extra layer of protection for customer data.
Regularly Update Software and Systems:
 Software and systems are not static; they evolve, and vulnerabilities are discovered over time. Hackers often target known vulnerabilities in outdated software. Therefore, it’s essential to keep all software up to date:
Software and systems are not static; they evolve, and vulnerabilities are discovered over time. Hackers often target known vulnerabilities in outdated software. Therefore, it’s essential to keep all software up to date:
Operating Systems: Regularly update your operating systems with security patches and updates provided by the software vendor.
Applications: Keep all applications and software used in your organization, including web browsers, office suites, and third-party applications, updated to the latest versions.
Firmware: Don’t forget about firmware updates for devices and network equipment, as vulnerabilities can exist at this level too.
Failure to update software and systems can leave your organization exposed to known security flaws that malicious actors can exploit. Automated patch management tools can help streamline this process and ensure timely updates.
Educate Employees:
 Human error is one of the leading causes of data breaches. Employees who are unaware of security risks and best practices can inadvertently compromise customer data. To mitigate this risk:
Human error is one of the leading causes of data breaches. Employees who are unaware of security risks and best practices can inadvertently compromise customer data. To mitigate this risk:
Phishing Awareness: Train employees to recognize phishing attempts. Phishing is a common tactic used by cybercriminals to trick individuals into revealing sensitive information or downloading malware.
Social Engineering Awareness: Educate employees about the various social engineering techniques that attackers use to manipulate them into divulging confidential information or performing actions that compromise security.
Password Management: Teach employees how to create strong passwords, the importance of not sharing passwords, and the risks of password reuse.
Incident Reporting: Encourage a culture of reporting security incidents promptly. Employees should know whom to contact if they suspect a security breach.
Regularly scheduled security awareness training and ongoing reminders can help reinforce these principles and make employees an active part of your security strategy.
Conduct Vulnerability Assessments:
 Regularly assessing vulnerabilities within your systems and infrastructure is essential to identify weaknesses that could be exploited by attackers. Vulnerability assessments involve:
Regularly assessing vulnerabilities within your systems and infrastructure is essential to identify weaknesses that could be exploited by attackers. Vulnerability assessments involve:
Scanning and Testing: Use specialized tools to scan your network and systems for known vulnerabilities. Vulnerability scanners can identify weak configurations, outdated software, and potential entry points for attackers.
Penetration Testing: Engage ethical hackers or penetration testers to simulate real-world attacks on your systems. They attempt to exploit vulnerabilities to uncover weaknesses in your security posture.
Prioritization: After identifying vulnerabilities, prioritize them based on severity and potential impact. This allows you to address the most critical issues first.
By proactively identifying and addressing vulnerabilities, you can reduce the likelihood of a successful attack on your customer data.
Use a Firewall:
 Firewalls are a critical component of network security. They act as a barrier between your internal network and external threats from the internet. Firewalls come in two main types:
Firewalls are a critical component of network security. They act as a barrier between your internal network and external threats from the internet. Firewalls come in two main types:
Network Firewalls: These filter traffic based on IP addresses and ports. They can block or allow traffic based on predefined rules.
Application Firewalls: These work at the application layer and can inspect the content of data packets, making them more effective at detecting and blocking sophisticated attacks.
A well-configured firewall helps prevent unauthorized access to your network and safeguards customer data from external threats.
Data Backups and Disaster Recovery:
 Data backups and disaster recovery planning are crucial for ensuring data availability and business continuity. Here’s what you should consider:
Data backups and disaster recovery planning are crucial for ensuring data availability and business continuity. Here’s what you should consider:
Regular Backups: Establish a routine backup schedule to ensure that customer data is regularly copied and stored in a secure location.
Off-Site Storage: Store backups in a location separate from your primary data center to protect against physical disasters like fires or floods.
Testing and Recovery Plan: Regularly test your backup and recovery procedures to ensure that you can quickly restore data in the event of a breach or system failure.
Having a robust backup and recovery strategy in place ensures that customer data can be recovered in case of data loss, minimizing disruption to your operations.
Secure Physical Access:
 Physical security measures are just as important as digital ones. Unauthorized physical access to servers or storage devices can lead to data breaches. To secure physical access:
Physical security measures are just as important as digital ones. Unauthorized physical access to servers or storage devices can lead to data breaches. To secure physical access:
Access Control Systems: Implement access control systems with card readers, biometric authentication, or PIN codes to restrict entry to sensitive areas.
Surveillance: Use security cameras to monitor critical locations and deter unauthorized access.
Visitor Logs: Maintain visitor logs to track who enters your facilities and why.
By securing physical access points, you reduce the risk of data breaches through unauthorized entry.
GDPR and Compliance:
 Depending on your industry and location, you may be subject to various data protection regulations, such as the General Data Protection Regulation (GDPR) or the Health Insurance Portability and Accountability Act (HIPAA). Compliance with these regulations is essential:
Depending on your industry and location, you may be subject to various data protection regulations, such as the General Data Protection Regulation (GDPR) or the Health Insurance Portability and Accountability Act (HIPAA). Compliance with these regulations is essential:
Data Mapping: Understand what customer data you collect, where it’s stored, and how it’s used.
Consent and Transparency: Ensure you have clear consent mechanisms for data collection and inform customers about how their data is processed.
Data Subject Rights: Be prepared to honor data subject rights, such as the right to access, correct, or delete their data.
Non-compliance with data protection regulations can result in significant fines and legal consequences.
Incident Response Plan:
 Despite all preventive measures, incidents can still occur. Having an incident response plan in place is critical:
Despite all preventive measures, incidents can still occur. Having an incident response plan in place is critical:
Notification Procedures: Define how and when you will notify affected parties, including customers, regulatory authorities, and law enforcement, in the event of a breach.
Containment and Remediation: Outline steps to contain the incident, identify the root cause, and remediate vulnerabilities to prevent future breaches.
Legal and PR Strategy: Plan how to manage legal aspects and public relations during and after an incident to minimize reputational damage.
An effective incident response plan helps you minimize the impact of a data breach and demonstrates your commitment to customer data security.
Final Thoughts
In a world where trust is the currency of customer relationships, the importance of data security cannot be overstated. Each measure we’ve explored is like a layer of armor, reinforcing your commitment to safeguarding customer data. By implementing these ten essential steps, you are not merely protecting sensitive information; you are demonstrating to your customers that their privacy and trust are your utmost priorities. So, as you embark on this journey of fortifying your data fortress, remember that each layer, each safeguard, strengthens the bonds of trust, securing not only your customer data but the future success of your business as well.
Dive deep into insights, tips, and the latest trends delivered straight to your inbox. Unlock exclusive content, be the first to know about our exciting updates, and join a community that thrives on innovation and growth.
Sign up for our newsletter now and never miss a beat in the dynamic world of business!
Subscribe Here:
We value your time and inbox space. Expect only the best from us, no spam included!
